Shares of consumer fintechs whipsawed while regulators tallied $19.7 billion in consumer relief and $5 billion in civil penalties through January 2025, a stark reminder that shipping fast without airtight controls can torch value overnight. PCI DSS v3.2.1 officially retired on March 31, 2024, with v4.0 becoming the industry standard and all v4.0 requirements turning mandatory by March 31, 2025, which means every release that touches card data now lives under a tighter bar for proof and process.
The tension is obvious and very current, yet the data shows speed and stability can rise together when teams pair modern DevOps with rigorous, risk‑based compliance programs that regulators themselves are pushing for in 2024 rulemaking. Investors want faster feature velocity and cleaner audits, consumers want fewer outages and faster refunds, and employees want guardrails that let them ship on Friday without sweating a Monday consent order, and that is the real game here.
After the hype cycle peak, the new reality is blunt: elite software teams increase deployment frequency and improve stability at the same time, while compliance moves from bolt‑on to built‑in via risk‑based controls that match system risk to program evidence, not the other way around. PCI DSS v4.0 tightens what “good” looks like for card data and makes compliance timelines unavoidable, so payment flows shift to tokenization, hosted fields, and vendor‑validated SDKs that shrink scope while preserving speed.
Stripe’s guidance reflects that shift through SAQ pathways, QSA support, and v4.0 readiness, which reduces local card exposure and keeps pipelines moving even as the bar rises for yearly attestation and continuous monitoring. Meanwhile, FinCEN’s proposed rule explicitly requires effective, risk‑based AML/CFT programs with board oversight and documented risk assessments, so fintech DevOps must surface controls in CI to demonstrate design and operating effectiveness, not just pass a point‑in‑time audit, and here’s the thing, that is the only way to scale without compliance drag.
Key Data
As of January 30, 2025, CFPB enforcement actions have resulted in $19.7 billion in consumer relief, 195 million people eligible for relief, and $5 billion in civil money penalties, which is why “move fast and break things” is not a strategy in financial services.
PCI DSS v3.2.1 retired on March 31, 2024. v4.0 is the new standard, and all v4.0 requirements become mandatory on March 31, 2025, compressing remediation windows for any app that touches PAN and pushing teams toward scope‑minimizing integrations.
The 2024 DORA analysis reiterates that throughput and stability can rise together, while also documenting mixed system‑level impacts from AI adoption, which means release discipline and rework control matter more than raw code generation speed.
From Data to Practice
Those enforcement totals and deadlines explain why leading fintechs now treat compliance as a performance constraint to optimize, not a gate to dodge, because penalties, restitution, and forced rewrites erase years of growth if controls lag shipping speed.
PCI v4.0’s timeline and scope pressure make vendor‑hosted inputs, tokenization, and validated SDKs the pragmatic path to keep releases frequent while shrinking the audit surface, which is why Stripe’s SAQ guidance and v4.0 notes show up in so many RFPs and architecture decisions in 2024 and 2025.
And since FinCEN’s proposed AML/CFT program rule codifies risk‑based design, boards now expect dashboards that tie release cadence to control efficacy, which smells like a governance gap if pipelines cannot produce evidence on demand.
How to USA Fintech Apps Ship Faster Without Breaking Compliance: A Step‑by‑Step Guide
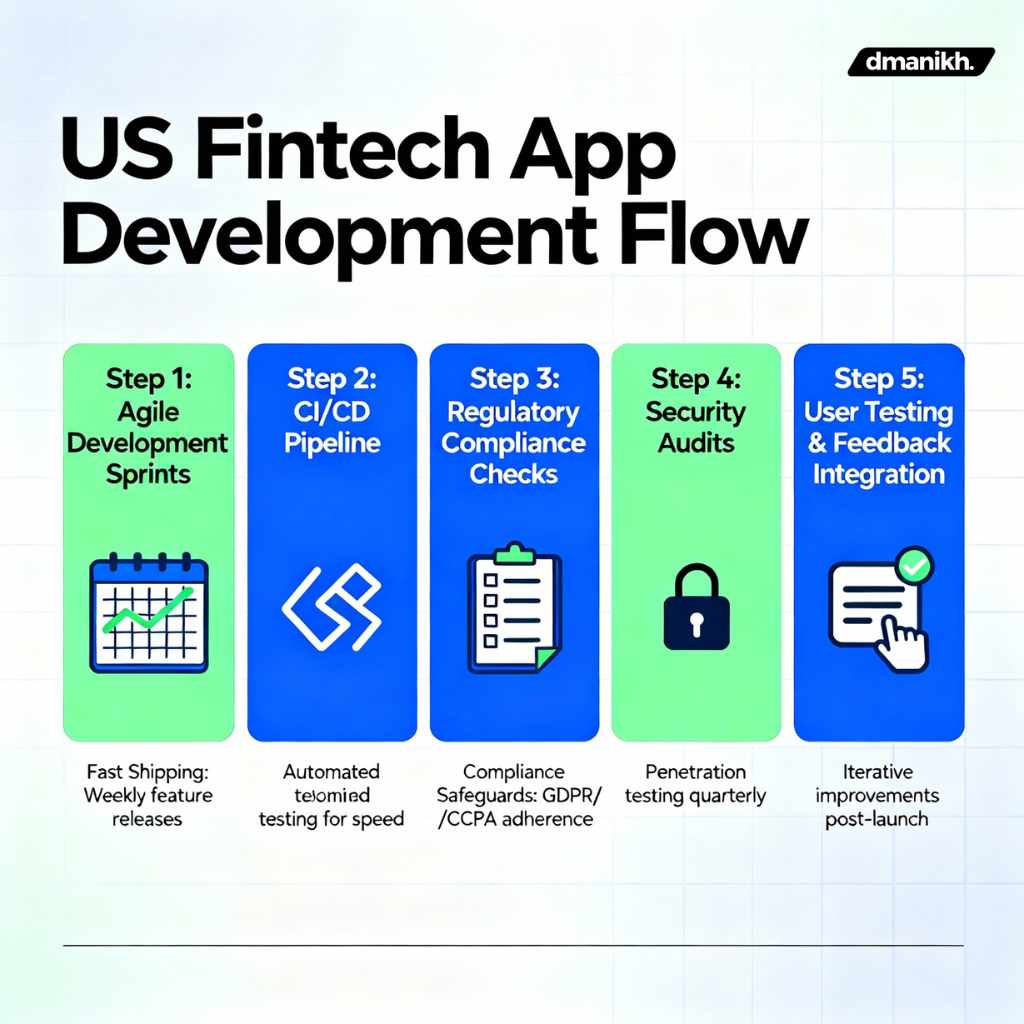
1. Redefine “Done” With Risk‑Based Controls
Shift “done” from feature complete to “feature complete with evidence,” anchored to the AML/CFT program elements regulators call out and the stability metrics that DORA correlates with elite performance. Build a simple risk assessment per change that tags flows by customer impact, data classification, and regulatory exposure, then require control mappings at PR time for items that touch payments or money movement, because evidence only shows up if you ask for it upstream.
Treat change‑fail and rework rate as first‑class stability signals in your CI logs, and make them visible to engineering leadership and the compliance owner so recovery time and defect cycles trend down as deployment frequency trends up. Align this definition with board‑approved AML/CFT program expectations since the proposed rule calls out board oversight, and keep it readable and fast to fill to hit the Hemingway‑style simplicity that workers actually use daily.
2. Minimize Scope With PCI-Friendly Patterns
Adopt hosted fields, tokenization, and mobile SDKs that prevent raw PAN from touching your servers, which makes SAQ A feasible for many integrations and reduces the blast radius of any incident while supporting weekly or even daily releases. Map each payment entry point to a least‑scope integration and document the SAQ path, QSA needs, and v4.0 changes that apply this year and next, since v3.2.1 is retired and v4.0 is the standard with a hard 2025 enforcement horizon.
Where you must handle card data directly, isolate those services, apply SAQ D rigor, and gate their deployment behind extra checks like dependency allowlists and secrets scanning to keep throughput high without letting toxic risk bleed into the wider app. Keep a running PCI remediation backlog tied to v4.0 deltas so engineering leaders see deadlines before audit windows close, which is how you maintain speed when surprise asks hit near quarter end.
3. Build Compliance Into CI/CD, Not Around It
Run IaC policy checks, SCA, SAST, and secret detection on every PR, but only fail the build on material violations tied to your risk tags to avoid alert fatigue while preserving a clean audit trail for control operation, and yes, sources say teams that tune these thresholds ship more consistently. Attach machine‑readable control IDs to pipeline steps so you can export a trace of “who approved what, when, and under which control,” which shortens regulator and partner bank reviews and keeps your Friday deploys viable.
Use canary and progressive delivery patterns to lower change‑fail rates and speed recovery time, because DORA’s message is that high frequency and high stability can be complementary when the system is instrumented for fast rollback and low rework. Capture post‑deploy checks that verify PCI scoping and AML/CFT watchlist rules executed as designed, so audit sampling is a search, not a scramble, which saves cycles and keeps sprint velocity intact.
4. Treat AI as an Assistant, Not a Throughput Guarantee
The 2024 DORA analysis documents that AI adoption has mixed system‑level effects despite perceived individual productivity gains, so constrain AI code suggestions with policy‑as‑code and gated merges to prevent rework spikes that quietly tax stability and speed. Focus AI on non‑deterministic toil like test generation and summarization rather than core business logic, then measure rework rate and MTTR to confirm the net effect is positive at the system level, not just in IDE snippets.
Keep a register of AI‑assisted changes that intersect with PCI scope or AML/CFT‑relevant logic so reviewers can scrutinize those diffs with control context and ensure no model artifact weakens required safeguards, which is both pragmatic and defensible. If metrics show rework creeping up as AI usage rises, pull usage back to the docs and tests layers until the pipeline’s stability improves, because DORA highlights that more code is not the constraint anymore, it’s safe flow into production that is.
5. Make Sponsor Banks and Regulators Your Allies With Proof, Not Promises
Banking partners and examiners want to see living systems that prove risk‑based design, which is exactly what FinCEN’s proposed rule emphasizes through risk assessment, internal controls, independent testing, and board oversight. Produce portal‑ready exports that show PCI v4.0 posture by integration type and SAQ, plus release metrics like deployment frequency, change failure rate, and time to restore for the past two quarters to demonstrate speed with safety, not rhetoric.
Given the post‑Synapse scrutiny, a growing coalition of fintechs and infrastructure firms is pushing voluntary compliance baselines, and public comments from leaders suggest that staffing compliance earlier shortens partner diligence and reduces launch risk, which keeps roadmaps on track. Close the loop by mapping consumer complaint handling and refund SLAs to pipeline dashboards to avoid CFPB scrutiny, since recent enforcement outcomes show how operational misses cascade into penalties and restitution at scale.
6. Close the Aml/Cft Loop in Product Flows
FinCEN’s proposed rule codifies the expectation that AML/CFT programs are effective, risk‑based, and reasonably designed, so wire your KYC, sanctions screening, transaction monitoring, and case management into product telemetry with thresholds tuned to customer risk. As BOI enforcement rolls out, align onboarding flows to beneficial ownership collection requirements and ensure data quality checks exist before account activation to prevent retroactive cleanups that slow releases and anger partners.
Normalize feedback loops between alerts and model thresholds so false positives fall without opening exposure, then document model governance and retraining cadence as part of the independent testing requirement to show the program is living, not static. Summarize all of this in a board‑level dashboard that ties risk posture to release velocity so leadership can make explicit tradeoffs with eyes open rather than reacting after an exam, which is how high‑performers sustain speed under scrutiny.
People of Interest or Benefits
“A former startup CEO told Forbes that in light of the regulatory changes over the past five years, any new fintech company should staff dedicated compliance before launching,” a sentiment echoed by the compliance coalition forming after the Synapse debacle that aims to set voluntary baselines akin to SOC 2’s role in security maturity, and the practical benefit is faster partner bank approvals and fewer last‑minute launch delays. That coalition proposes annual AML training for all employees and a designated BSA officer, which fits FinCEN’s emphasis on named responsibility and board oversight and reduces the chance that compliance debt balloons just as growth accelerates.
Looking Ahead
By March 31, 2025, PCI DSS v4.0 requirements are mandatory, so apps that still pass raw PAN through custom forms will face heavy SAQ D burdens or rushed refactors that jeopardize velocity in Q1 and Q2, which is preventable with hosted fields and validated SDKs today. CFPB’s enforcement tallies show that consumer harm tied to refunds, disclosures, or dispute handling remains expensive, so teams that wire operational SLAs into release criteria will dodge the worst outcomes and earn trust with regulators and partner banks.
In enterprise fintech, vendors are launching tools that let sponsor banks monitor program compliance for fintech partners in near real time, which means evidence‑ready pipelines will become a competitive advantage when negotiating partnerships and capital. FinCEN’s modernization push will likely harden expectations for risk assessment and innovation that reduces illicit finance, and teams that show how their AI and DevOps choices improve outcomes will shape the playbook rather than absorb it late.
Closing Thought
If elite teams can raise throughput and stability together while proving risk‑based design to regulators on demand, the only real question is whether the next big U.S. fintech winner will be crowned by faster features or by a faster evidence engine, and leadership will notice which one actually moves the multiple first.





